Assess security blind spots with our CYBERESIST and CYBERCREDS platforms
CYBERESIST®: AN AUTOMATED AUDIT PLATFORM FOR YOUR EXTERNAL AND INTERNAL ATTACK SURFACES
CYBERESIST® detects security vulnerabilities that attackers could exploit, providing a comprehensive security assessment.
Using intelligent testing, the platform conducts an in-depth analysis of risks, including potential attack vectors, and proposes corrective action plans.
FEATURES
01
Attack surface mapping
CYBERESIST® identifies all applications and services in use, including those that are not listed in the inventory or have not been officially approved (shadow IT). This mapping helps you understand your infrastructure, optimise resource management and strengthen security.

02
Searching for data leaks
CYBERESIST® identifies all applications and services in use, including those that are not listed in the inventory or have not been officially approved (shadow IT). This mapping helps you understand your infrastructure, optimise resource management and strengthen security.

03
Audits carried out without any impact
CYBERESIST® audits do not require any probes, agent installation or event log collection, ensuring rapid implementation with no impact on the performance of your infrastructure or the integrity and protection of your sensitive data.
04
Automated audit of attack surfaces
CYBERESIST®< 2 >detects vulnerabilities by performing passive and active tests on internal and external attack surfaces to analyse each component, providing a detailed analysis whilst minimising duplicates and false positives, with precise identification of security flaws (100+ families, correlation and prioritisation).

05
Professional reports & action plan
CYBERESIST® provides comprehensive dashboards featuring a cyber score, an executive summary with a prioritised action plan, a detailed list of vulnerabilities, and recommended remediation solutions. Reports can be exported in French or English in Word, Excel and PDF formats.

06
Monitoring and tracking the gaps
Once the fixes have been implemented, CYBERESIST® carries out a check to verify that the issues have been resolved and to track progress between audits.
100% AUTOMATED TESTS
80+ integrated tools. Comprehensive testing without manual intervention.
CORRELATION & SORTING
Fewer duplicates and a massive reduction in false positives.
AUTOMATED REPORTS
List of vulnerabilities with Cyberscore, action plan, in French or English.
Detect compromised access before an attacker can exploit it
CYBERCREDS® : PLATEFORME DE DÉTECTION ET SURVEILLANCE DE VOS ACCÈS COMPROMIS
CYBERCREDS® is a passive monitoring platform that detects compromised access and identifies the attack vectors involved.
It does not store any passwords in plain text and never tests detected access points.
We process data in accordance with the GDPR.
FEATURES
01
CYBERCREDS in a nutshell
Infostealers silently infect your employees’ workstations. They export credentials and session data to underground Telegram channels. CYBERCREDS detects compromised access within your organisation: infected machine, affected employee, date, and compromised access.

02
Exposure detection
For each detection related to your domain, here is the information displayed.
The credentials are partially masked — only the reuse pattern is visible.
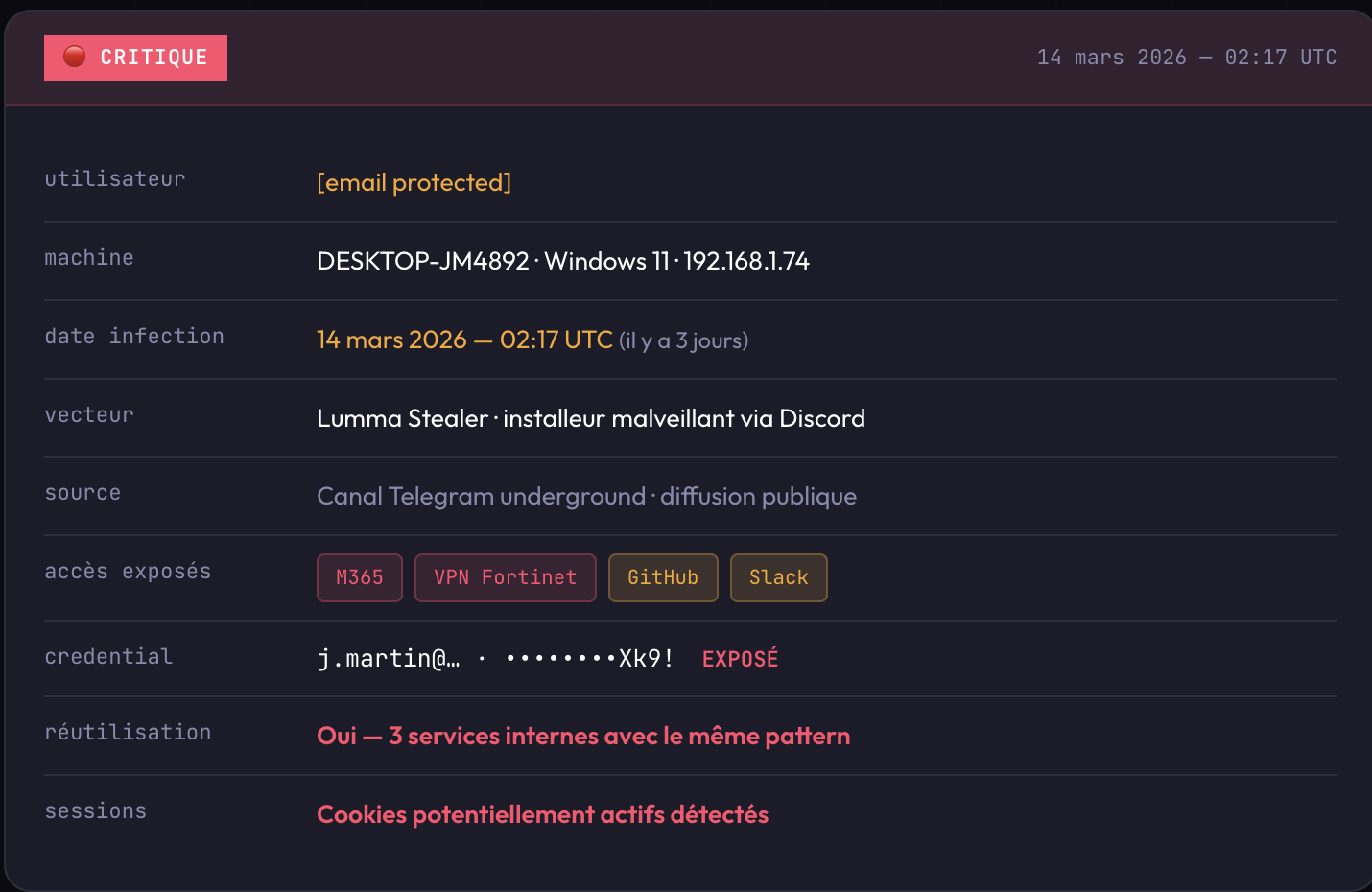
The platform alerts you when an account has been compromised and identifies the method used. It does not store any passwords in plain text and never attempts to access the accounts it detects. Your teams retain control over the actions to be taken.
03
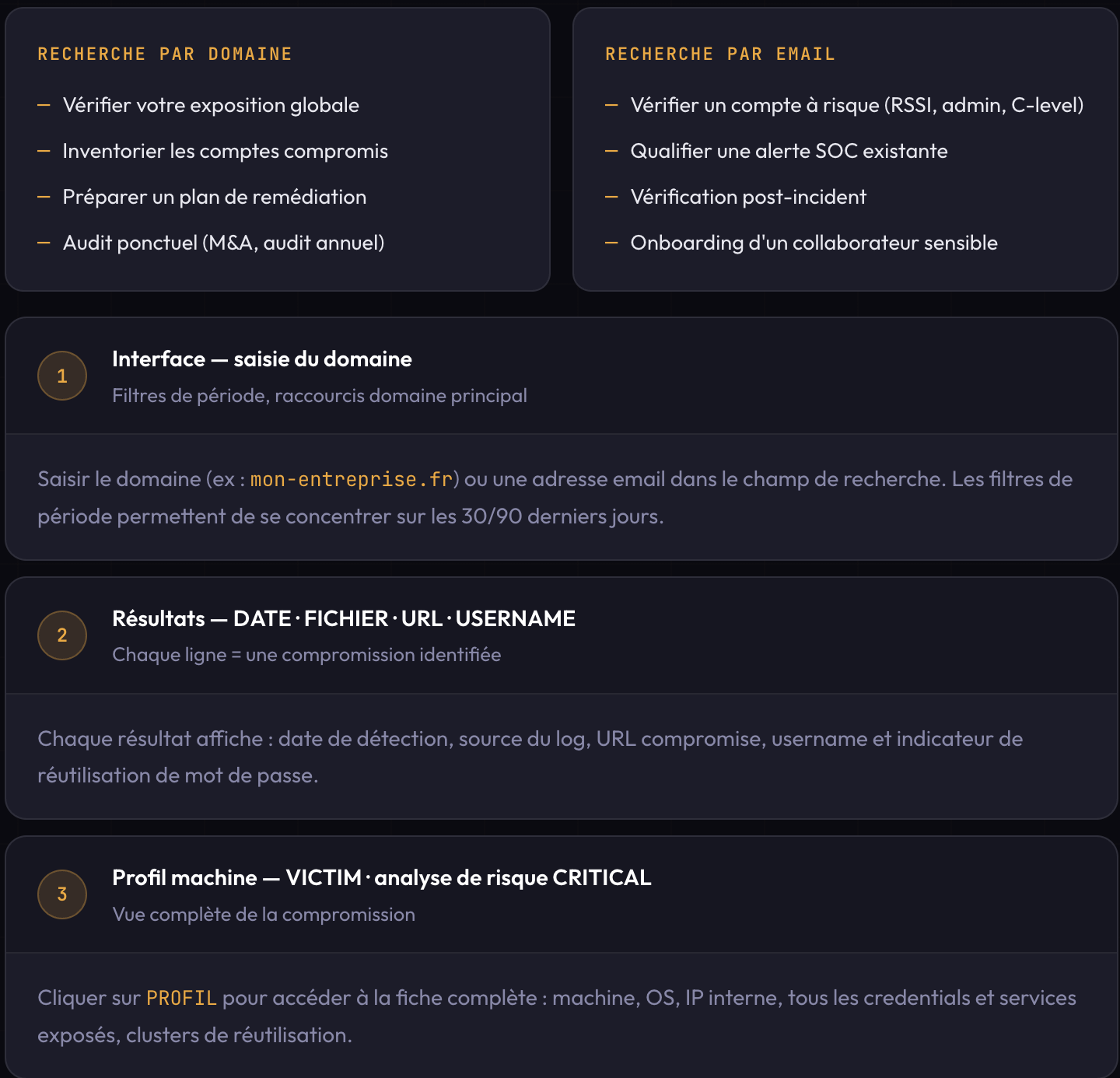
Quick search
With CYBERCREDS, you can search the database in real time for a domain or email address.
Results in seconds, including date, URL, username and source file. Each row is clickable to view the full machine profile: date of compromise, country, CRITICAL/HIGH risk analysis, and reuse clusters.
04
Domain Intelligence
Analyses all logs for your domain and creates a comprehensive risk map: compromised identities, exposed services, discovered internal infrastructure, password reuse and top URLs.
Can be exported as an HTML report ready to send to your SOC or CISO.

05
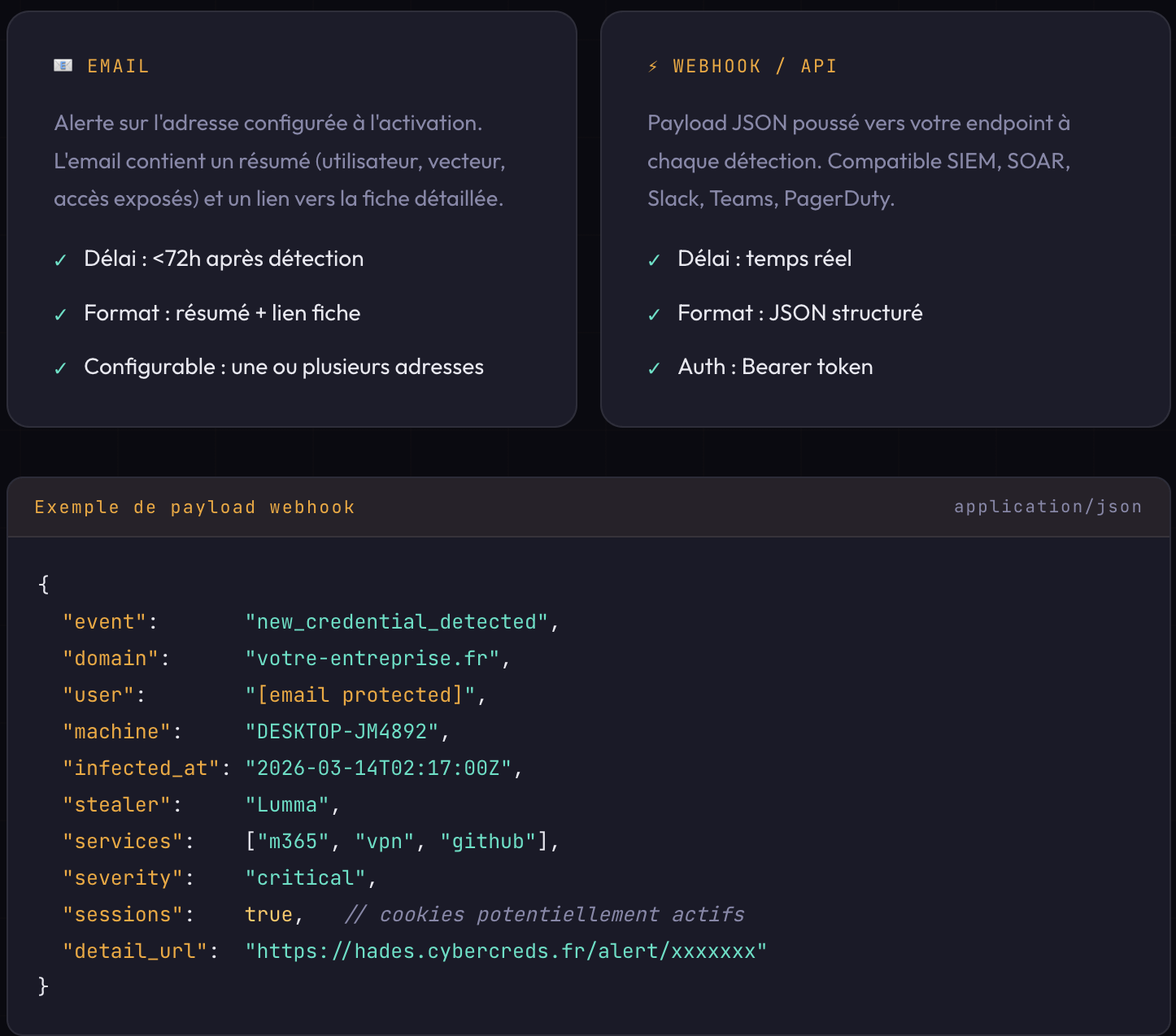
Notifications
Active monitoring keeps a constant watch over your domain.
As soon as a matching log is detected, you are alerted.
Maximum time limit: 72 hours.
Critical alerts are notified within the first hour.
06
API integration
The REST API allows you to integrate detection results directly into your SOC stack: querying the database, retrieving active alerts, and downloading reports.

MSP & MSSP editions
You are an MSP or MSSP and you want to perform regular security checks for your customers.
We invite you to use dedicated instances of CYBERESIST and CYBERCREDS with your teams.
Your customers benefit from a complete cybersecurity solution by working directly with your company.
Strengthen your position as a trusted partner by generating additional revenue
PROSPECTING
Integrated prospecting tools
based on risk analysis.
CLIENT ONBOARDING
Domains, scopes, AD, OSINT
in just a few minutes.
ORCHESTRATION
Nmap, Nuclei, OpenVAS, ZAP
orchestrated according to your playbooks.
MULTI-TENANT
Customer portal
easy to use.
SECURE INFRASTRUCTURE
Hosted in France
(OVH).
API INTEGRATION
SOC/SIEM integrations
Alert workflows.
They trust us